Internet Research Project
- By Jacquelin Ng -
Risks to Privacy
Some data privacy risks are identity theft, data breaches, phishing scams, and online tracking. Companies that keep personal information should be responsible for keeping their customer’s data safe. Both individuals and companies should be considerate of privacy when collecting or storing personal information.
Also, some risks to privacy from storing personal information is the possibility of a shared computer. For example, schools and workplaces often share computers among many people. If an individual does not sign out of their account, their personal information is at a high risk of being stolen. It is important to use public networks or computers safely.
Large corporations that store massive amounts of personal information are at high risks of cyberattacks. If the corporation doesn’t have enough safeguards, it can result in a major leak of sensitive information like an individual’s personally identifiable information (PII), which are often related to finances and social security numbers. This can create a huge domino effect that compromises millions of people's personal information.
Computing Resources
Computing resources can be misused to create scams, identity theft, or fraud. However, it can be protected by being careful when you are entering personal information. Social media is a common resource that is often misused by oversharing because once something is on the internet, it never really goes away. Computing resources can be misused for many reasons, often by people with malicious intentions.
AI is constantly misused to create deepfakes and spread false information. This is a huge example of a computing resource that is misused. The rapid increase of public use of AI resulted in less protection, which evolved into data breaches and compromised security.
Computing resources can be protected by being cautious on what information you share online. People should always use strong, unique passwords that they can memorize. It can help prevent hackers from stealing personal information. People can protect themselves by not oversharing on social media, AI products, and public networks.
Unauthorized Access
Unauthorized access can be gained by using stolen information, breaking security measures, and exploiting weaknesses in a system. Usually, the hackers use the system to steal, alter, or destroy information. It is a major cybersecurity risk that threatens the safety of personal data, networks, and systems.
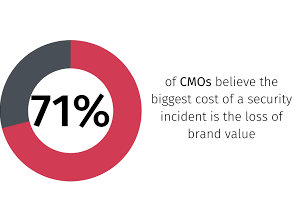
If personal information gets out, it is very difficult to remove it. If there is not enough protection against unauthorized access, it can compromise security and degrade a company’s reputation. This can cause a permanent loss of credibility and eventually customers. Sometimes, cybercriminals can threaten national security if the data breach is serious.
Cyber attacks and unauthorized access can make stolen data accessible to other hackers. This can cause a long-term effect of fraudulent activities and identity theft. It is important to identify and avoid scams at a minimum to protect your own personal information. In addition, take extra precautions before entering any personal data into a website or application. Unauthorized access can be gained easily, but it can be prevented by taking careful measures to protect yourself.
Harms and Benefits
Computing innovations can be helpful to quickly connect people and deliver messages effectively. The internet allows us to rapidly share ideas, and helps humanity finish tasks faster. It also helps with everyday life such as security cameras, which allow us to monitor our homes. Computing innovations can create a very positive impact on our lives if we use them responsibly and carefully.
Computing innovations can be harmful because it can cause social anxiety and misuse of information. For example, social media can cause sleep deprivation and an increase of anxiety. Also, AI has become increasingly harmful because some people use it to do the work for them without learning. This can result in plagiarism, false information, and degrading a person’s work ethics. AI is harmful because it often doesn’t check its own information before showing it to the users.
Unintended consequences can be both positive or negative. For example, the World Wide Web expanded to public use, providing social networks. However, the initial internet for the World Wide Web was for scientists to share research information quickly. A negative unintended consequence is cyberbullying. The rapid spread of the web resulted in major impacts because it became uncontrollable. This can happen when a programmer or developer doesn’t consider the negative consequences before rapidly sharing it. Computing innovations can be harmful and helpful due to intended and unintended consequences.